To our list of long-time friends Windows, Ubuntu, Android, iOS, and macOS, we now welcome Chrome OS. Gotta catch ‘em all! We are happy to report that Prey, the security tool you need to stay in control of your remote assets and their data is now available for all Chromebook laptops to be prepared if your devices get stolen, are breached, or go missing.
The power of Chromebooks
Chromebooks are an excellent, compact option for student devices. The reason for this comes from three defining traits: affordability, software potential, ease of use, and administration. To begin with, schools can easily tackle a classroom’s laptop fleet for as low as $150 per Chromebook.
These devices can also be purpose-built for classrooms, making them an ideal choice for educational settings. They are compact, lightweight, and durable, designed to withstand the rigors of student use. With their intuitive Chrome OS, students can seamlessly transition from one device to another, fostering a consistent and familiar learning experience.
The need for Chromebook tracking and protection
Ensuring the safety of Chromebook data is of utmost importance, especially in educational environments. With the rise of remote learning and the increasing reliance on digital tools, protecting student data has become a priority.
Safeguarding student information not only helps comply with regulations like FERPA (Family Educational Rights and Privacy Act), but it also ensures the trust and confidence of parents and guardians in the educational institution's ability to protect sensitive data.
Prey for Chromebook
Prey’s Chromebook Tracking solution is a Chromebook-specific application compatible with all native Chrome OS laptops and available through Chrome Web Store. Oh, and keep in mind that Prey offers a comprehensive solution to track and protect not only Chromebooks but also a wide range of devices across multiple operating systems. With Prey, you can now manage devices and secure them using a single account.
Chromebooks need tracking just like any other device to ensure that they are safe.
Prey for Chromebook tracking features
Tracking stolen or lost Chromebooks can be a challenge specially if you have to manage thousands of students devices and your are one solo band but Prey's powerful tracking capabilities make it easier to locate and find lost/stolen/rogued devices. Prey's tracking and geo-fencing capabilities can be a lifesaver in such situations.
Once you deploy Prey in your Chromebook device, you’ll be able to enjoy our tried and tested array of features:
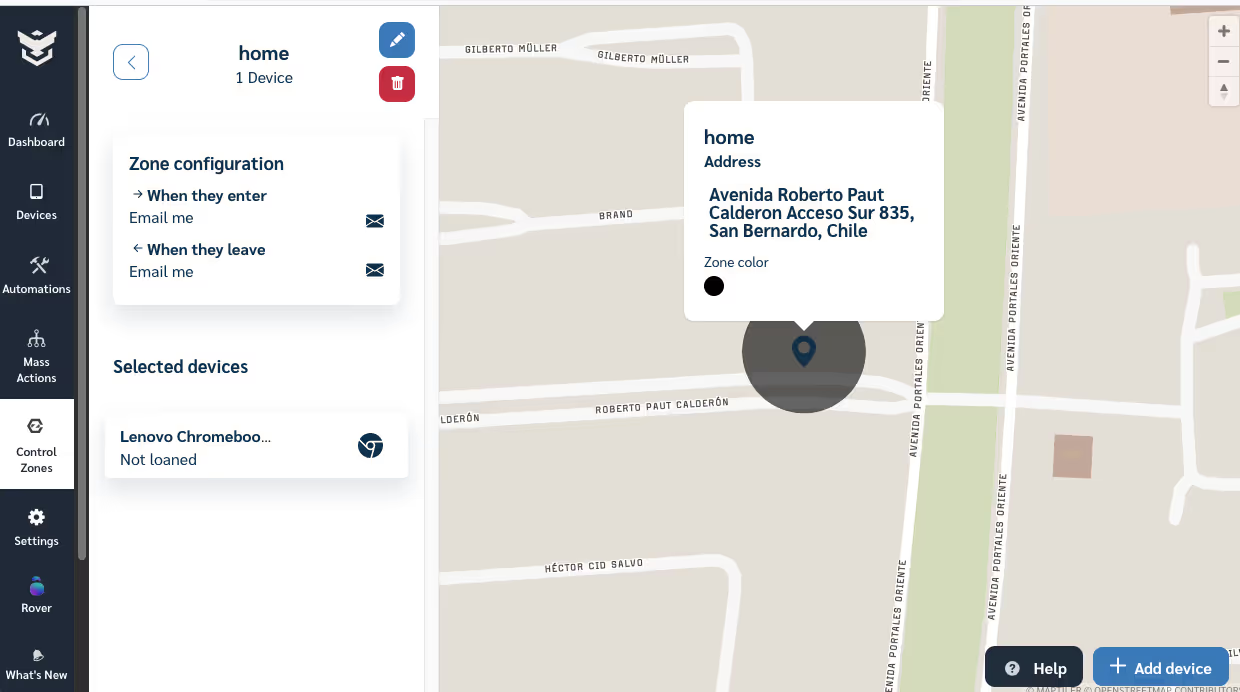
Creating and managing Geo-fences
With Prey, you can create and manage geofencing control zones, or virtual boundaries, for your Chromebooks. You can set up specific locations where your devices should be, such as the school premises. If a Chromebook leaves or enters these zones, you'll receive notifications, allowing you to take immediate actions like receive and send alerts.
Always-on device location tracking *
Prey provides always-on device location tracking, giving you real-time updates on the whereabouts of your Chromebooks. Whether it's a lost device or a suspected theft, you can quickly locate the device and initiate the necessary steps to recover it.
* We understand the importance of student privacy. That's why you can disable this feature at any time and re-enable it in case of a security incident.
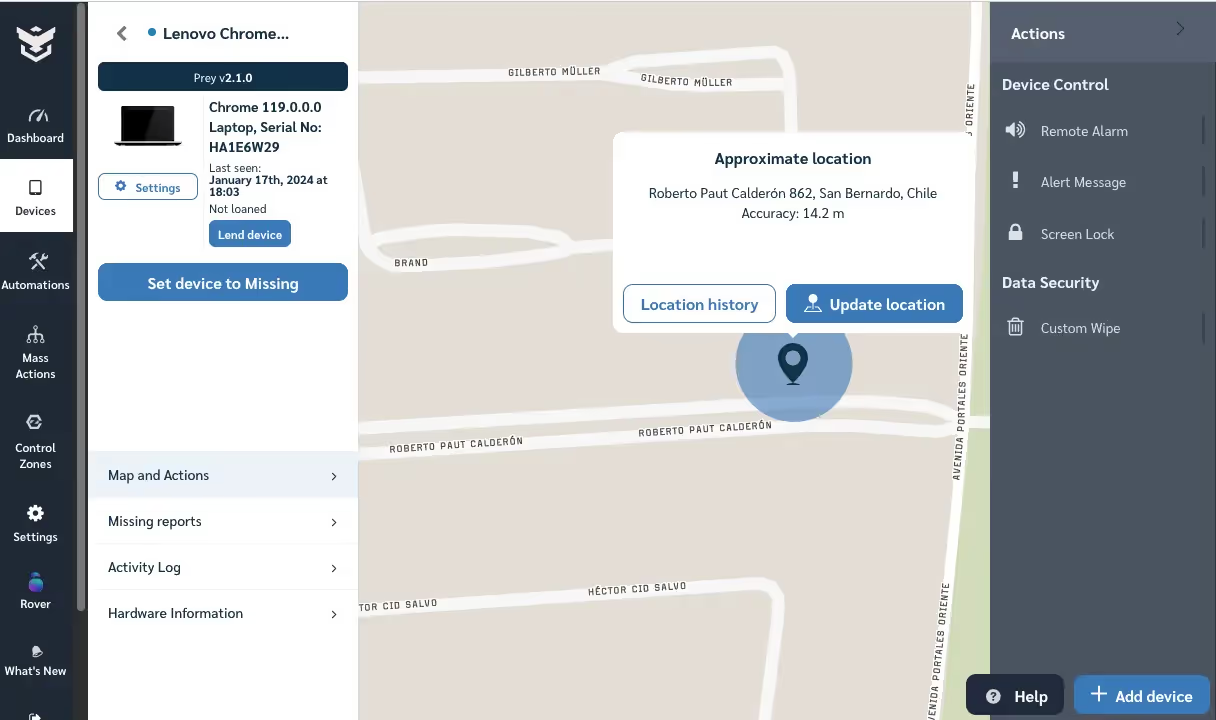
Remote alerts and alarms
Prey enables you to send remote alerts and alarms to your Chromebooks, effectively communicating important messages regarding their safety. Whether it's a gentle reminder to return the device or a loud alarm to deter unauthorized use, you have control over the communication.

Custom Wipe
Prey empowers IT managers with the capability to remotely wipe Chromebooks using specific parameters. This feature proves invaluable for restoring devices to their original state for maintenance purposes or preparing them for allocation to new students following the conclusion of their previous owner's usage period.

Screen lock
IT managers have the ability to remotely secure Chromebooks with Prey. This is a valuable tool for preventing misuse, suspicious activities, or securing lost or stolen devices. This capability ensures the thwarting of unauthorized access, thereby safeguarding student and staff data from potential third-party breaches.

Missing Reports: Screenshots, location, and Chrome information *
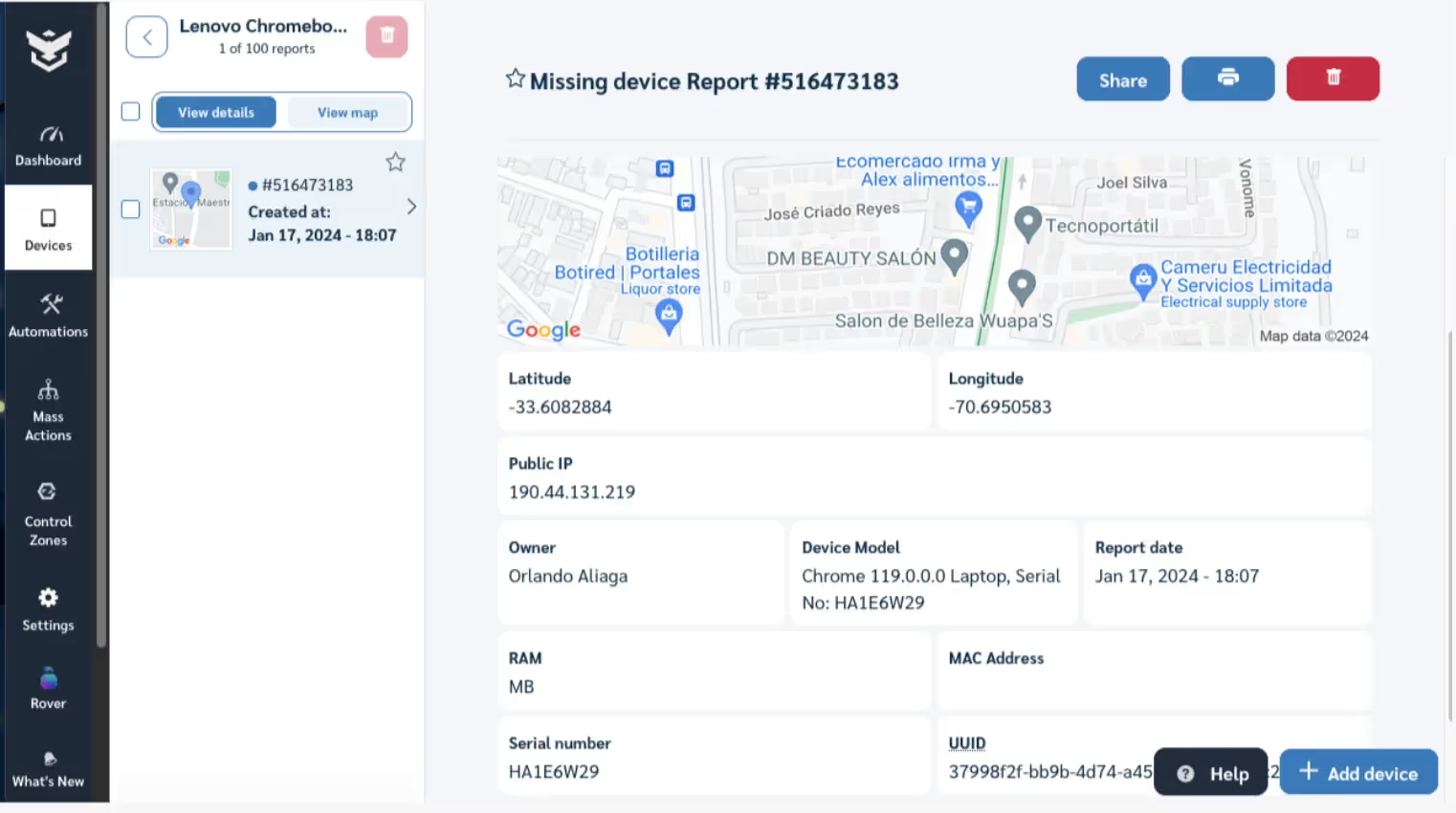
Prey generates comprehensive missing reports that provide detailed information about your Chromebooks. From screenshots of the device's current state to precise location coordinates and Chrome browser information, these reports offer valuable insights for troubleshooting, recovery, and ensuring the safety of your devices.
* We understand the importance of student privacy. That's why you can disable this feature at any time and re-enable it in case of a security incident.

How can these tracking features help your school
Picture this: A sneaky student decides to "borrow" their friend's Chromebook without permission. Little do they know, the device is armed with Prey's tracking capabilities. As they try to make a quick getaway to a location outside a designated safe zone, a geo-fence is triggered and an alert is shown on the administrator's device.
You can almost hear the Mission Impossible theme song playing as the student realizes their little prank has been foiled. After receiving an alert, the school's device administrator can send a notification to the missing device telling it to return it.
But, what if that student doesn't trigger an alarm linked to a geo-fence, and just hides the Chromebook? In this case, once the administrator gets notified about the missing device, they can check its location, then call the proper authorities to retrieve it.
So, with Prey, if a Chromebook goes missing, you'll have a wealth of information at your fingertips, like a detective with a virtual magnifying glass.
Bonus track: Chromebook 1:1 management
As you may know, Prey is not just a tracking tool. We want to help school IT admins streamline their device lending program. Our device management tool simplifies the checkout process, ensuring that devices are assigned and tracked properly, all in one place. With this feature, you can assign users and timeframes for loans, receive notifications, and automate security actions for different timeframes and geolocation scenarios to reduce the risk of loss or theft.
Say you have a couple of Chromebooks with loans overdue, with Prey you can choose to send alert messages. Time is of the essence when dealing with remote hardware.
Prey is also a great ally to wrap up your program’s school year. Return devices to Factory Reset status remotely and in a couple of clicks and get set for the upcoming semester.
With Prey, you can rest assured that your devices are secure and your checkout program is streamlined. And don't forget, our tool is not limited to Chromebooks but can be used for all your devices across multiple operating systems.
Special pricing for schools
Affordability is key for every organization, especially if that friendly price tag involves the features you require to get the job done. Educational institutions can take advantage of Prey's special pricing, tailored to meet the unique needs of schools. Prey recognizes the importance of education and provides special pricing for educational organizations. Visit our EDU hub here to know more about all the advantages we give to educational organizations.
To learn more about how to install Prey for Chromebooks using Google Admin Console, please visit our comprehensive step-by-step installation guide.


