Resource Hub
Your one-stop IT knowledge center. Here you'll find the tools, guides & best practices for device management excellence.

Editor's picks

Don’t leave your data security to chance. Get the technical guide to containing, triaging, and reporting lost corporate laptops in under 24 hours.
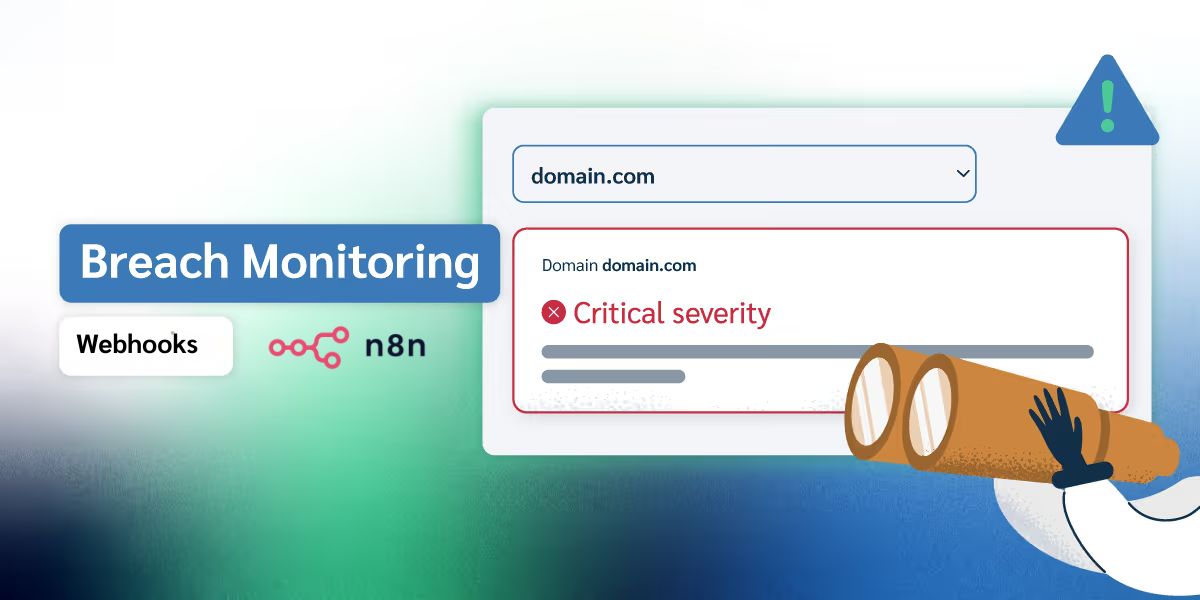
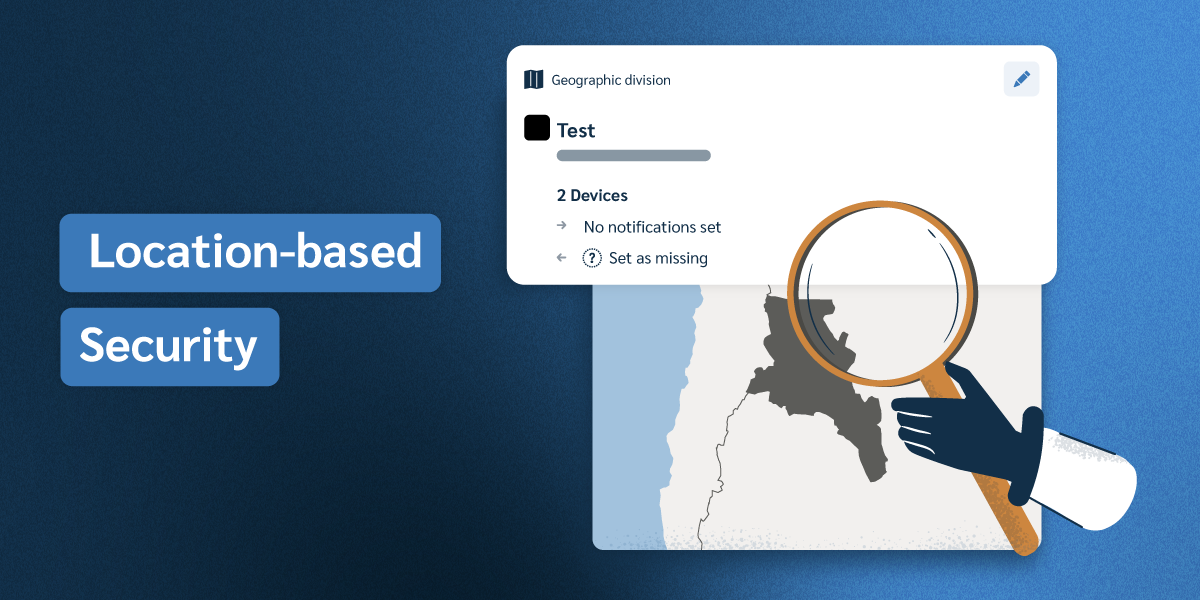
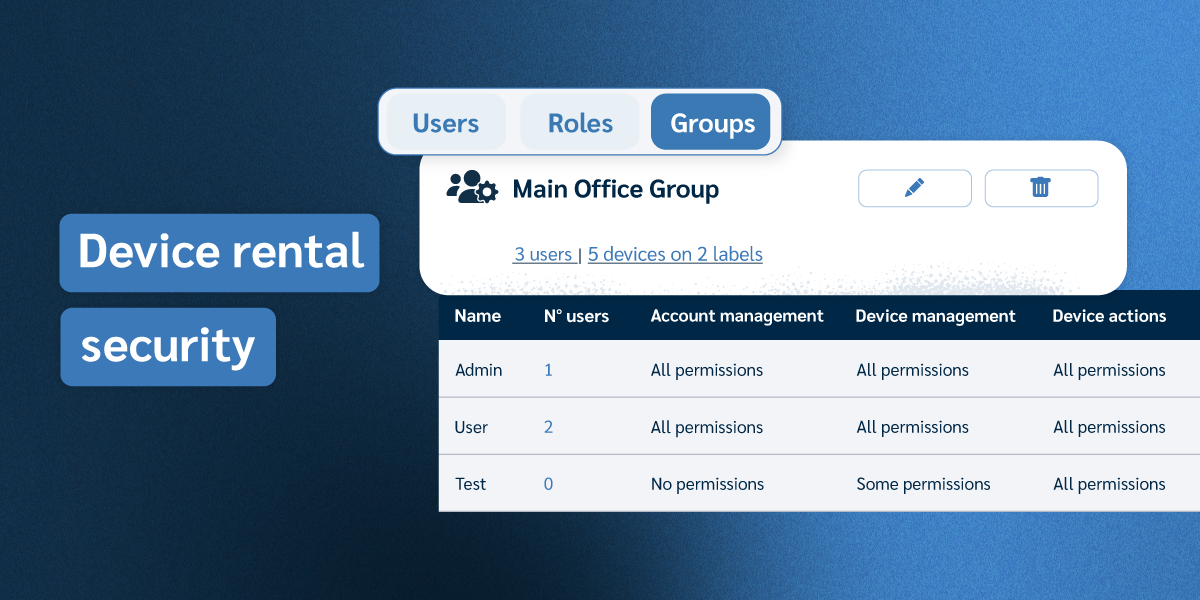
Discover Prey’s 4-layer security approach: device tracking, remote protection, asset management, and dark web breach monitoring, all in one platform.
Prepare, secure, and deploy your school’s devices before day one with this IT-focused back-to-school checklist.
Stop back-to-school 1:1 device chaos: audit, automate & secure every K-12 laptop with Prey
Product Guides
Explore Prey's powerful solutions. Comprehensive overview of features, benefits & pricing options.
White Papers
Learn how to secure & manage devices effortlessly. Expert tips for IT Pros!
Reference Kits
Curated presentations and checklists to help IT teams quickly understand security best practices, compliance requirements, and device management essentials.