Compliance isn't about having a policy, it's about proving the policy runs every day, on every device. Prey turns security rules into automated actions: geofences that trigger lock or wipe when a device leaves an approved zone, audit logs that track every admin move, and missing reports with timestamped evidence when things go wrong. Location history stretches back up to 12 months, giving you the paper trail auditors actually ask for

Compliance and enforcement
More resources
Monitor entire company domains for leaked credentials on the dark web, built for organizations with large teams and multiple email addresses.

Learn how to flag a missing device, gather evidence for recovery, review activity logs, and trace location history.
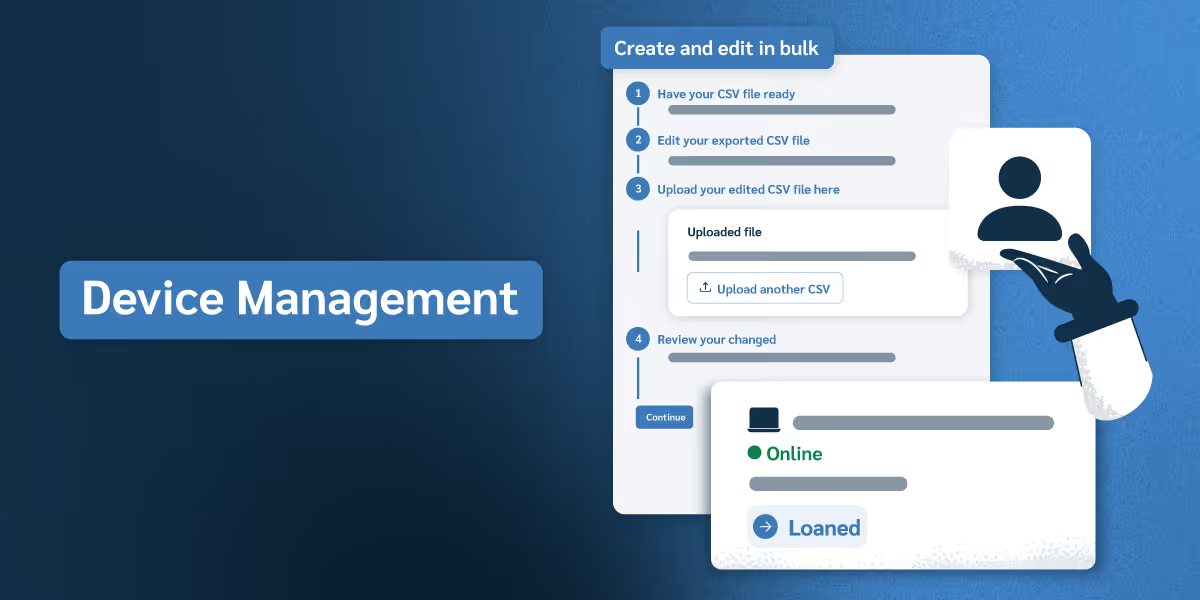
Explore how to organize devices, manage user roles, track asset checkouts, and maintain audit-ready records across your organization.